DMARC
3aMedia recently added a new customer domain onto one of our dedicated servers on Liquid Web and for some strange reason the domain’s emails were flagged for DMARC. It led to an interesting discussion about DMARC and what it is so we thought we would weigh in.
DMARC (Domain-based Message Authentication, Reporting & Conformance) is the newest check in email authentication. But, like SPF (Sender Policy Framework) and DKIM (Domain Keys Identified Mail), it’s sometimes difficult to understand. That’s why we’re dedicating a post to explaining how it works, and why it matters.
What it is: DMARC ensures that legitimate email is properly authenticating against established DKIM and SPF standards, and that fraudulent activity appearing to come from domains under the organization’s control (active sending domains, non-sending domains, and defensively registered domains) are blocked. Two key values of DMARC are domain alignment and reporting.
How it works: DMARC’s alignment feature prevents spoofing of the “header from” address by:
- Matching the “header from” domain name with the “envelope from” domain name used during an SPF check, and
- Matching the “header from” domain name with the “d= domain name” in the DKIM signature.
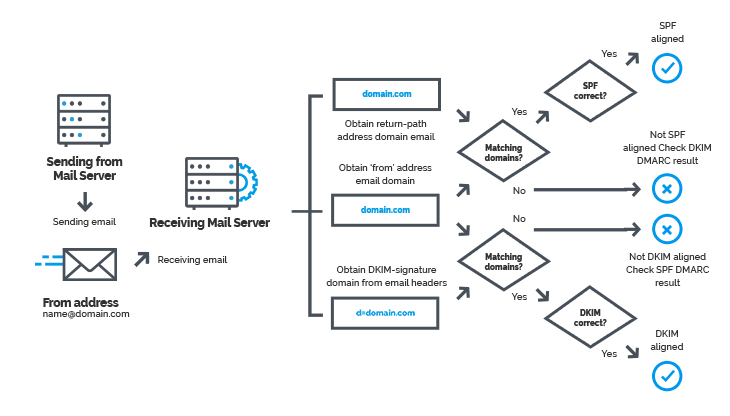
To pass DMARC, a message must pass SPF authentication and SPF alignment and/or DKIM authentication and DKIM alignment. A message will fail DMARC if the message fails both (1) SPF or SPF alignment and (2) DKIM or DKIM alignment.
DMARC allows senders to instruct email providers on how to handle unauthenticated mail via a DMARC policy, removing any guesswork on how they should handle messages that fail DMARC authentication. Senders can either:
- Monitor all mail, to understand their brand’s email authentication ecosystem, and ensure legitimate mail is authenticating properly without interfering with the delivery of messages that fail DMARC
- Quarantine messages that fail DMARC (e.g., move to the spam folder)
- Reject messages that fail DMARC (e.g., don’t deliver the mail at all)
Mailbox providers send regular DMARC aggregate and forensic reports back to senders, giving them visibility into what messages are authenticating, what messages are not, and why.
Why it matters: DMARC is the first and only widely deployed technology that can make the “header from” address (what users see in their email clients) trustworthy. Not only does this help protect customers and the brand, it discourages cybercriminals who are less likely to go after a brand with a DMARC record. If you want to read more, please read about email handling on 3aMedia.
